When you sit down at your company computer at the start of each day, chances are you enter a password to log on to the network. Perhaps you enter another password to access your e-mail or an internal database that contains important financial, customer or other proprietary data that must be protected at all costs.
You might think that a strong password is enough to keep your company’s data safe from theft and unauthorized intrusions. But given the fact that millions of passwords are hacked every year, to truly keep your data safe from theft you need to employ additional security measures.
One of the most effective means of keeping out intruders is to use two factor authentication. Stronger than a single password, which can be guessed, revealed or hacked, a system that uses this type of software requires users to supply more than one form of identification before gaining access to the system. Well-designed authentication software makes it virtually impossible for a remote hacker to access the system via password, therefore protecting your company from a costly data breach.
Something You Know and Something You Have
Multi-factor authentication, also known as TFA-2, is not a new concept; most people have used it hundreds of times in their lives without even realizing it. Every time you use an ATM, you use this security technology.
TFA-2 involves providing at least two pieces of information in order to gain access to the data or system. There are three types of information to choose from: something you know, such as a password or security question; something you have, such as a token, a smartcard or identification card; and something that you are, which means providing some type of physical evidence of your identity, such as a fingerprint.
When you use the ATM, the system combines the “what you have” and “what you know” requirements. You insert your ATM card into the machine, indicating that you have an account with the bank and are authorized to make transactions, and then a password, to prove your identity. The system isn’t always foolproof as criminals have been known to steal both cards and passwords; still, for the vast majority of banking customers, the TFA-2 system keeps their money safe from theft via the ATM.
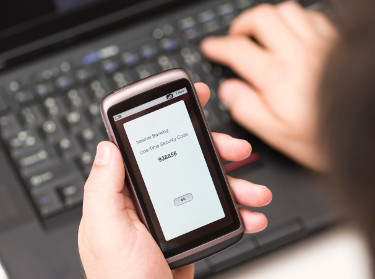
On a computer network, the process is the same. By using both a password — which is developed either at random or by following current protocol for strong password creation — and a physical security item, such as a PIN-protected security token that the user inserts into the machine to gain access to data and networks, organizations can prevent their information from falling into the wrong hands.
It’s important to note that multi-factor authentication is not the same as strong authentication. Some banks or organizations require users to answer a challenge question or provide personal data, such as a portion of their Social Security number to gain access to the system. While these systems do provide an extra layer of protection, they are not considered true multi-factor authentication, as they only use one type of criteria: what the user knows.
More Than Just Smart Security
The most common multi-factor authentication security systems are like ATM machines, combining the “what you know” and “what you have” criteria. Biometric systems that authenticate users based on a fingerprint, eye scan or other biological traits tend to be expensive, especially for small businesses.
However, two-factor authentication systems are affordable and secure, and with more and more organizations employing mobile technology in their businesses, as well as using cloud servers and allowing remote access to their systems via laptops, the extra layer of protection that such a system provides is money well spent. In fact, the United States Federal Financial Institutions Examination Council guidelines have called for such systems since 2005, and there is speculation that multi-factor authentication security will soon become the law for any business dealing with personal data.
Today there is a wide array of multi-factor authentication systems available, so it’s important to compare the software options to determine which is best suited for your company’s needs. For example, some software is better suited for onsite applications than for remote access, while some solutions allow for automatic encryption and digital signatures on transferred data. However, in the wake of a number of high-profile security breaches, and the high costs associated with such breaches, it’s important for all companies to use the security tools available to stop criminals in their tracks.















